A Quiet Espionage Campaign Built on Aging Hardware
State-sponsored hackers tied to Russia's military intelligence apparatus have been quietly abusing well-known security flaws in aging Internet routers to harvest authentication tokens from Microsoft Office users at massive scale. Security researchers and Microsoft both disclosed the operation today, warning that the campaign compromised routers on more than 18,000 networks without ever deploying a single piece of malware.
Microsoft's own blog post identified more than 200 organizations and 5,000 consumer devices caught up in the surveillance dragnet, which was constructed by a threat actor the company tracks as Forest Blizzard—also widely known as APT28 and Fancy Bear.
Who Is Forest Blizzard?
Forest Blizzard is attributed to military intelligence units operating within Russia's General Staff Main Intelligence Directorate (GRU). The group has a long and well-documented history of high-profile intrusions. Most notably, APT28 was responsible for compromising the Hillary Clinton presidential campaign, the Democratic National Committee, and the Democratic Congressional Campaign Committee in 2016 as part of a broader effort to interfere with the U.S. presidential election.
How the Attack Worked: DNS Hijacking at Scale
Researchers at Black Lotus Labs, the security division of Internet backbone provider Lumen, tracked the campaign and found that at its peak activity in December 2025, Forest Blizzard had ensnared more than 18,000 routers. The vast majority of targeted devices were unsupported, end-of-life models—or devices that had fallen far behind on security updates. The routers were primarily older Mikrotik and TP-Link devices aimed at the Small Office/Home Office (SOHO) market.
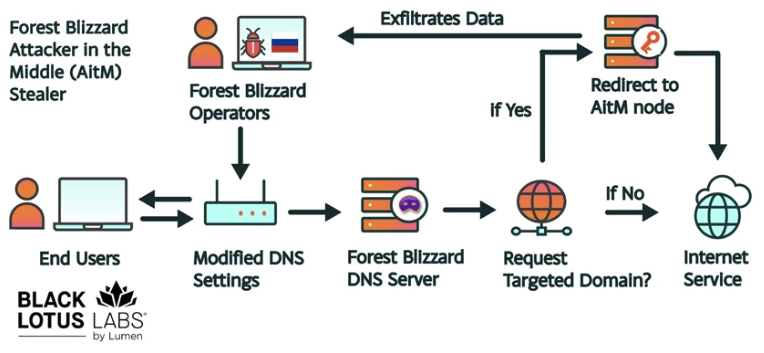
Black Lotus Security Engineer Ryan English explained that the attackers did not need to install any malicious software on the compromised routers. Instead, they exploited known vulnerabilities to alter each device's Domain Name System (DNS) settings, substituting the legitimate DNS servers with servers under the attackers' control. Those rogue servers were hosted on a small number of virtual private servers operated by Forest Blizzard.
As the U.K.'s National Cyber Security Centre (NCSC) notes in a new advisory on Russian router compromise activity, DNS is the foundational system that allows users to reach websites by typing familiar addresses rather than numeric IP addresses. By hijacking DNS at the router level, the attackers were able to propagate their malicious settings to every device on the local network simultaneously.
Stealing Tokens Without Phishing Credentials
The most significant consequence of this DNS manipulation was the interception of OAuth authentication tokens—the digital credentials that Microsoft Office services issue after a user has already successfully logged in, including after completing multi-factor authentication (MFA). Because these tokens are only transmitted post-login, stealing them allowed Forest Blizzard to access victim accounts directly, bypassing the need to phish individual passwords or one-time codes entirely.
Microsoft described the Forest Blizzard activity as using DNS hijacking "to support post-compromise adversary-in-the-middle (AiTM) attacks on Transport Layer Security (TLS) connections against Microsoft Outlook on the web domains." While the company acknowledged that targeting SOHO devices is not a new tactic, Microsoft stated this marks the first time it has observed Forest Blizzard "using DNS hijacking at scale to support AiTM of TLS connections after exploiting edge devices."
English offered a candid assessment of why the technique was effective despite its relative simplicity:
"Everyone is looking for some sophisticated malware to drop something on your mobile devices or something. These guys didn't use malware. They did this in an old-school, graybeard way that isn't really sexy but it gets the job done."
Primary Targets: Government and Sensitive Institutions
According to the new Lumen report, Forest Blizzard primarily directed this capability at high-value institutional targets, including:
- Government agencies
- Ministries of foreign affairs
- Law enforcement bodies
- Third-party email providers
The scale of the operation—reaching over 18,000 networks—suggests the group cast a wide net, exploiting every vulnerable router it could identify rather than restricting itself to carefully selected victims.
Tactical Shift After Earlier NCSC Disclosure
Black Lotus Labs engineer Danny Adamitis noted that Forest Blizzard has shown a consistent pattern of rapidly adapting its tactics in response to public exposure. Following a similar NCSC report published in August 2025, the group made a significant pivot. At that time, Forest Blizzard had been using malware to control a far smaller, more carefully selected set of compromised routers. The day after that August report was released, the group abandoned the malware-based approach and shifted to the mass DNS-manipulation strategy described in today's disclosures.
Adamitis told KrebsOnSecurity: "Before the last NCSC report came out they used this capability in very limited instances. After the report was released they implemented the capability in a more systemic fashion and used it to target everything that was vulnerable."
Adamitis added that it will be notable to watch how Forest Blizzard responds to today's wave of public attention directed at its current operation.
Regulatory Backdrop: The FCC's Router Security Push
The campaign arrives amid heightened U.S. regulatory concern about the security of foreign-manufactured routers. TP-Link, one of the device brands prominently targeted in the Forest Blizzard operation, had previously been the subject of discussions about a complete U.S. sales ban. On March 23, the U.S. Federal Communications Commission (FCC) went further, announcing it would no longer certify consumer-grade Internet routers manufactured outside the United States.
The FCC stated that foreign-made routers had become an untenable national security threat, warning that poorly secured devices represent "a severe cybersecurity risk that could be leveraged to immediately and severely disrupt U.S. critical infrastructure and directly harm U.S. persons."
Critics and industry experts have pushed back, arguing that the new policy would leave very few consumer-grade routers available for purchase domestically—with one notable potential exception being Starlink satellite Internet routers, which are manufactured in Texas. The FCC has said that router makers may apply for a special conditional approval from either the Department of War or the Department of Homeland Security, and clarified that the policy does not affect routers that consumers have already purchased.
What Users and Administrators Should Do
Security experts are urging both home users and IT administrators to take immediate action to reduce exposure to the techniques Forest Blizzard has deployed at scale. Recommended steps include:
- Replace end-of-life or unsupported routers with actively maintained models
- Apply all available firmware updates to router hardware immediately
- Verify that router DNS settings have not been altered from trusted, known-good values
- Monitor for unexpected OAuth token activity in Microsoft 365 and related services
- Consider network segmentation to limit the blast radius of any SOHO device compromise
The fact that Forest Blizzard achieved widespread intelligence collection without deploying malware underscores that hardening the network edge—not just endpoint devices—is a critical and often neglected element of organizational security.
Source: Krebs on Security