A Botnet Crashes Into an Anonymity Network
Since early February 2026, the Invisible Internet Project (I2P) — a decentralized, encrypted network engineered to anonymize online communications — has been struggling under the weight of an unintended assault from the Kimwolf botnet. What began as an attempt by Kimwolf's operators to route their command-and-control traffic through I2P turned into a week-long disruption that left the network operating at roughly half its normal capacity.
Kimwolf first emerged in late 2025 and spread at a remarkable pace, compromising millions of poorly secured Internet of Things (IoT) devices — including TV streaming boxes, digital picture frames, and routers — and conscripting them into a platform capable of launching abnormally large distributed denial-of-service (DDoS) attacks.
What Is I2P and Why Was It a Target?
I2P describes itself as a privacy-focused, censorship-resistant network built for private websites, messaging, and data sharing. As the project's own website explains,
"It works by routing data through multiple encrypted layers across volunteer-operated nodes, hiding both the sender's and receiver's locations."
That architecture makes I2P attractive to activists, journalists, and privacy-conscious users worldwide — but it also makes it appealing to threat actors seeking a resilient fallback for botnet command-and-control infrastructure that is difficult for security teams and network operators to dismantle.
According to I2P's Wikipedia page, the network is composed of roughly 55,000 computers distributed around the globe, with every participant serving simultaneously as a router relaying traffic and as a client. However, Lance James, founder of the New York City-based cybersecurity consultancy Unit 221B and the original founder of I2P, told KrebsOnSecurity that current real-world participation is considerably lower — somewhere between 15,000 and 20,000 devices on any given day.
February 3: Users Notice Something Is Wrong
On February 3, I2P users began filing complaints on the organization's GitHub page about tens of thousands of routers abruptly flooding the network. Reports described a rapidly accelerating number of new routers joining in rapid succession, yet these nodes were incapable of transmitting data. The sheer volume of inbound connections overwhelmed the network to the point where legitimate users could no longer reach one another.
The severity of the problem was captured in one exchange on GitHub, where a user asked whether the network was under attack. Another participant replied:
"Looks like it. My physical router freezes when the number of connections exceeds 60,000."
I2P developers shared a graph illustrating a pronounced drop in successful connections coinciding precisely with the moment Kimwolf began attempting to use the network as a fallback communications channel.
Kimwolf's Operators Admit the Mistake
On the same day the outages began, the individuals controlling Kimwolf posted openly to their Discord channel, acknowledging that they had inadvertently disrupted I2P after attempting to join approximately 700,000 Kimwolf-infected bots as nodes on the network. The admission came in a Discord channel that, notably, bore the name of journalist Brian Krebs.
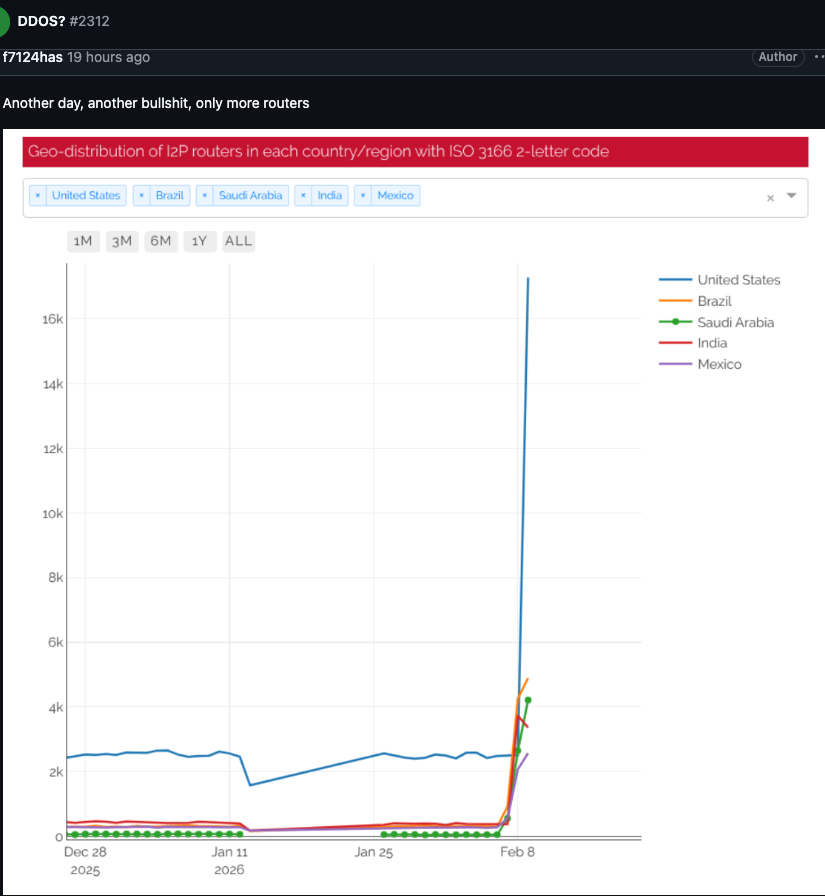
A graph posted by an I2P user on February 10 showed tens of thousands of routers — the majority originating from the United States — attempting to join the network in a short window of time.
Understanding the Sybil Attack Dynamic
While Kimwolf is primarily known as a DDoS weapon, the disruption it caused to I2P this week falls into a different threat category: a Sybil attack. In a Sybil attack, a single entity subverts a peer-to-peer network by creating and controlling a massive number of fake or pseudonymous identities, overwhelming the system's ability to distinguish legitimate participants from malicious ones.
The scale of Kimwolf's incursion made the attack especially damaging. Even using the more conservative estimate of 15,000 to 20,000 active I2P nodes, the 700,000 Kimwolf bots that attempted to join represented many multiples of the network's entire normal population.
A Pattern of Disruption: Cloudflare and Tor
Benjamin Brundage, founder of Synthient — a startup that tracks proxy services and was the first to document Kimwolf's unique spreading techniques — explained that Kimwolf's operators have been actively searching for command-and-control infrastructure that cannot easily be neutralized through coordinated action by security companies and network operators.
Brundage noted that the botnet's controllers have been experimenting with both I2P and the Tor anonymity network as backup command-and-control channels. No widespread disruptions to the Tor network have been reported as of yet.
"I don't think their goal is to take I2P down," Brundage said. "It's more they're looking for an alternative to keep the botnet stable in the face of takedown attempts."
This is not Kimwolf's first brush with major internet infrastructure. Late last year, the botnet created significant problems for Cloudflare after its operators instructed millions of infected devices to route traffic through Cloudflare's domain name system (DNS) settings. The maneuver caused Kimwolf's control domains to repeatedly displace Amazon, Apple, Google, and Microsoft at the top of Cloudflare's public ranking of the most frequently requested websites.
Internal Turmoil May Be Weakening the Botnet
Despite the chaos Kimwolf has caused, there are signs that the operation is becoming less stable from within. Brundage said the botnet's leadership appears to have recently driven away some of its more capable developers and operators, a development he believes contributed directly to the rookie miscalculation that disrupted I2P.
The fallout has been measurable: the botnet's overall infection count has dropped by more than 600,000 systems in a short period.
"It seems like they're just testing stuff, like running experiments in production," Brundage said. "But the botnet's numbers are dropping significantly now, and they don't seem to know what they're doing."
Recovery Underway for I2P
Lance James confirmed that I2P is still running at roughly half its normal capacity in the wake of the incident. Developers are rolling out a new software release that is expected to deliver stability improvements for users over the coming week. The episode underscores the vulnerability of small, volunteer-run privacy networks to being inadvertently — or deliberately — overwhelmed by the sheer scale of modern botnets.
Source: Krebs on Security